Businesses with multiple locations face unique security challenges. Coordinating protocols, responding to incidents, and maintaining consistent protection across various sites can be daunting. Yet, with the right approach and tools, these challenges can be transformed into opportunities for enhanced security and operational efficiency.
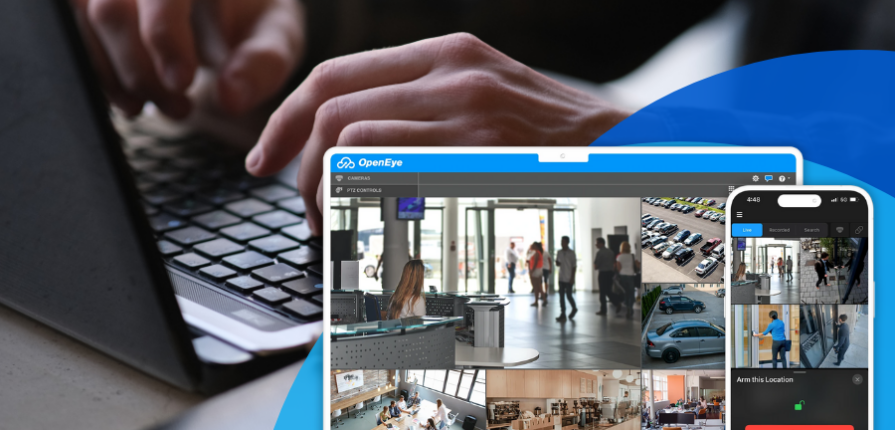
Cloud-based platforms have emerged as game-changing solutions for multi-location security management. These systems offer centralized control, real-time monitoring, and data analytics capabilities that span all your locations. Let’s examine how these platforms work and the benefits they bring to businesses.
Centralized Control: The Cornerstone of Multi-Site Security
At the heart of effective multi-location security lies centralized control. Cloud-based security platforms allow security personnel to manage all sites from a single interface. This centralization eliminates the need for on-site security management at each location, reducing staffing costs and ensuring consistent security protocols across the organization.
These platforms enable security teams to:
- Set and modify access rights across all locations simultaneously
- Update security protocols and procedures company-wide with a few clicks
- Manage and monitor all security devices, from cameras to access control systems, through one dashboard
The power of centralized control becomes evident during critical situations. Imagine a scenario where a security threat is identified at one location. With a centralized system, security personnel can immediately lock down affected areas, alert local authorities, and implement emergency protocols across all sites if necessary – all from a single command center.
Real-Time Monitoring: The Key to Rapid Response
Real-time monitoring capabilities offered by cloud-based platforms provide an unprecedented level of situational awareness. Security teams can view live feeds from any camera at any location, receive instant alerts about potential security breaches, and track the movement of people and assets across all sites in real-time.
This real-time visibility allows for:
- Immediate detection and response to security incidents
- Proactive threat prevention through early warning systems
- Efficient allocation of security resources based on real-time needs
Consider a retail chain with stores across the country. With real-time monitoring, the central security team can quickly identify a shoplifting incident at one location and coordinate with local staff and law enforcement for a swift response. Simultaneously, they can analyze patterns to determine if similar incidents are occurring at other locations, allowing for a coordinated, company-wide response if needed.
Data Analytics: Turning Information into Actionable Insights
The true power of centralized security management lies in its ability to collect and analyze data from all locations. Advanced analytics tools can process this vast amount of information to uncover patterns, predict potential security risks, and provide valuable insights for business operations.
Key benefits of security data analytics include:
- Identifying trends in security incidents across locations
- Optimizing security staffing and resource allocation based on historical data
- Generating comprehensive reports for compliance and insurance purposes
For example, a hotel chain might use analytics to identify peak times for security incidents at each property. This information could be used to adjust staffing levels, implement additional security measures during high-risk periods, and even inform business decisions such as adjusting check-in times or implementing new guest policies.
Implementing Centralized Security Management: Key Considerations
While the benefits of centralized security management are clear, implementation requires careful planning. Here are some key considerations:
- Scalability: Choose a platform that can grow with your business, easily accommodating new locations and technologies.
- Integration: Ensure the platform can integrate with your existing security hardware and software across all locations.
- Customization: Look for solutions that allow you to tailor the system to your specific business needs and security protocols.
- Training: Invest in comprehensive training for your security team to maximize the benefits of the new system.
- Cybersecurity: With increased connectivity comes increased cyber risk. Ensure your centralized system has robust cybersecurity measures in place.
Multi-Location Security Management
Centralized security management solutions offer a powerful way to address the complex security needs of multi-location businesses. By providing centralized control, real-time monitoring, and data analytics capabilities, these platforms not only enhance security but also contribute to overall business efficiency and intelligence. As businesses continue to expand and evolve, the role of centralized security management will only grow in importance, serving as a crucial tool for protecting assets, employees, and customers across all locations.